
According to Business Insider Intelligence, “$6 trillion will be invested in the Internet of Things (IoT) between 2015 and 2020, which will yield $12.6 trillion ROI over the next decade”
For the past few years these predictions have been discussed and the whole industry has been looking at IoT as the next big Industrial revolution, implying a radical change and an entirely new paradigm for a connected planet.
Since the Mirai botnet attack in 2016, we have seen a dramatic increase in the number and the sophistication of attacks targeting IoT devices. For example, the Satori IoT botnet in 2018 compromised hundreds of thousands of IoT devices. As we are embracing IoT in true enterprise class use cases across many industries including healthcare, industrial and automotive, we realize that an IoT security breach goes beyond simple data loss, or DDoS, it is very much a critical safety issue, with potentially disastrous impact.
Many analysts, industry experts and government regulators are now talking about security as the big impediment for IoT value realization, and as a result there are policies and best practice guidelines being formed.
This means the compelling economic and social benefits are at risk as we do not have a universal security framework that can address all the challenges and concerns. We need to make sure we get IoT security right from the start to realize its full potential. Everyone, including Governments, regulatory bodies and standards groups are being forced to rethink this issue.
Existing security solutions have evolved as an afterthought and may work for some closed platforms and less critical consumer IoT use cases but fail to protect the true Enterprise class IoT solutions. The leading IoT Platform vendors such as AWS, PTC and Microsoft often talk about security as a shared responsibility, however the challenges of device and data security is often left to the customers to figure out. And whilst there have been some early attempts to solve these security challenges, many have only focused on one piece of the solution, and not the end-to-end solution and real-world use cases and the security business challenges that arise. We now have an opportunity to redefine the security model that can work for Enterprise IoT use cases and open platforms and we call this Enterprise IoT security 2.0
In March 2018, the UK government published a report titled “Secure by Design: Improving the cyber security of consumer Internet of Things Report”. In 2019, members of US Congress introduced the IoT Cybersecurity Improvement Act of 2019, to help improve cybersecurity for IoT Devices. Accelerating HIPAA, GDPR, CCPA compliance for American companies, National Institute of Standards and Technology (NIST) has published a new guide for manufacturers of IoT devices to assist them is ensuring that adequate cybersecurity measures are in place so that the devices are secure from threats when users link them to the Internet.
As articulated above, security incidents, compliance requirements, safety measures and government regulations are forcing the industry to move towards a Secure by design and Privacy by Design approach. Recently, there has been many announcements by big vendors, Intel, Microsoft, Arm to address these challenges. E.g. Intel SDO (Secure Device Onboard), Microsoft Sphere.
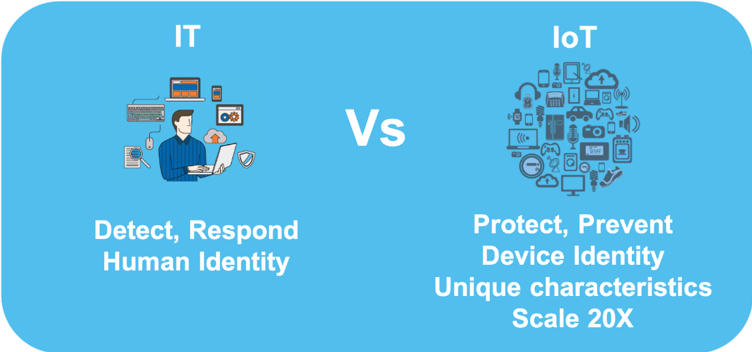
All these policies and guidelines still do not provide a comprehensive Enterprise IoT Security framework that can be implemented. IoT use cases are all about the data. While existing IT security models adopting a network centric approach still provide some value, the new model moves to a device and data centric approach. More specifically there needs to be a device-bound data security model that is trusted, based on proven technologies and automated processes to deal with the IoT scale.
At Device Authority we have experience implementing many critical IoT solutions in Healthcare, Industrial IoT and Automotive sectors, and working with our ecosystem partners we have published a comprehensive Enterprise IoT Security Model that addresses the defense in depth required to prevent the security breaches, operate at scale and achieve compliance.
Please download our updated Enterprise IoT Security 2.0 Blueprint model for more details.
