Situation
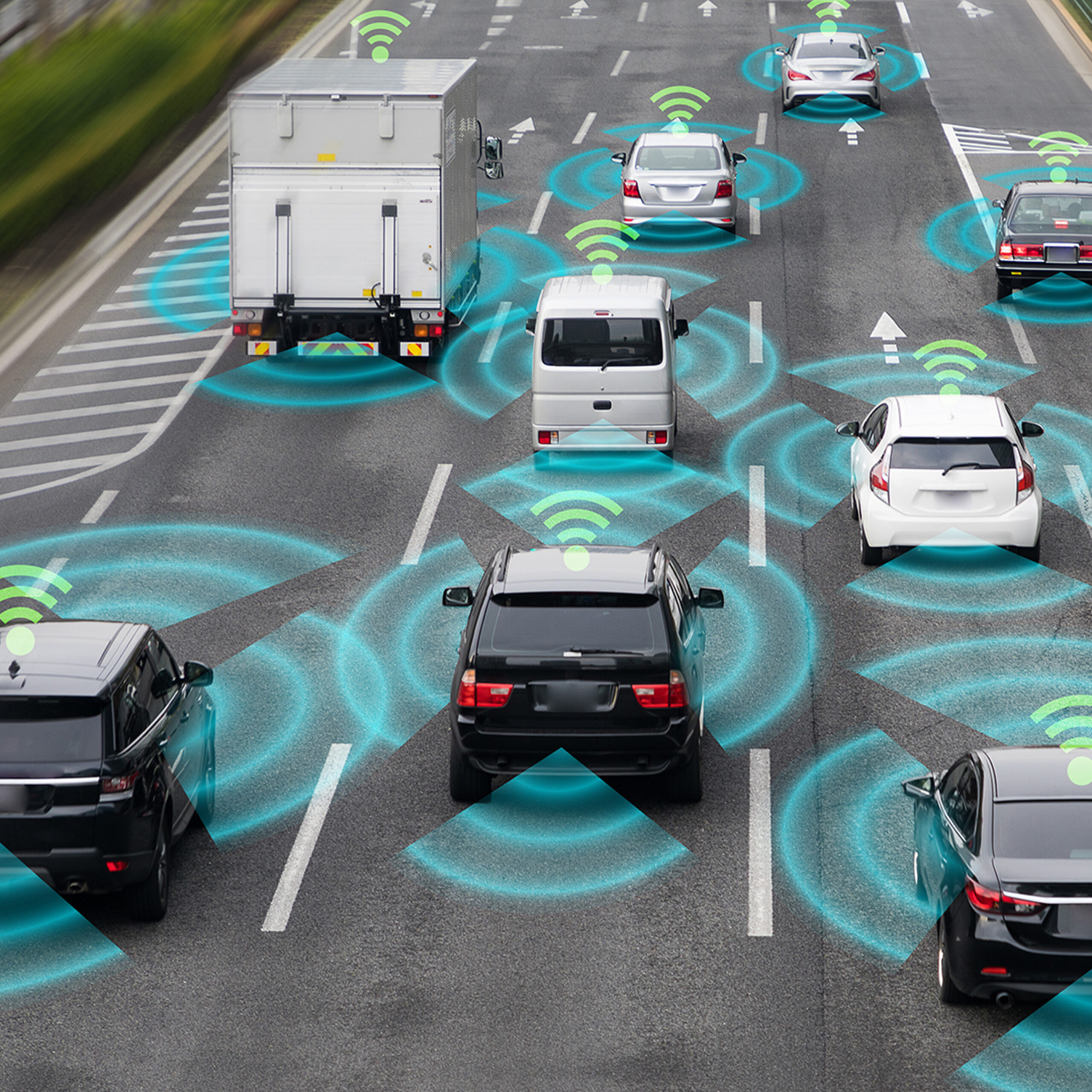
A major vehicle manufacturer utilizes PKI Certificates for vehicle identity, authentication to network services, and data encryption. Throughout the vehicle’s lifetime ownership needs to be securely transferred if the vehicle is sold or leased to a new owner, requiring a new certificate to be securely provisioned to the vehicle.
This requires PKI-based security and Automated Identity Lifecycle Management for the vehicle and its connected applications.
Solution
Device Authority’s KeyScaler is used to provide:
- PKI Services for IoT with Automated Identity Lifecyle Management including certificate provisioning, renewals, and revocations for connected vehicles
- KeyScaler trust anchor technology for vehicle Telematics Control Unit (TCU)
- KeyScaler Security Suite for automated integration with Microsoft Azure IoT and Connected Vehicle Platforms